Banning geoblocking - based
Forcing websites to be transparent about cookies - based
Forcing websites to apply proper data security - based
Forcing Apple to use usb c - based
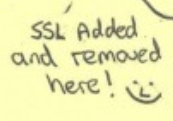
Ending end to end encryption - fucking clowns
Ending streaming service geoblocking - back on track, hopefully?
what those posts have in common is that they’re both about EU attempts to reduce the power of US tech companies. (In the first they’re reducing those companies’ power to violate privacy, and in the second they’re reducing their power to protect it.)
Nobody spies on our citizens but us
The second one makes no sense to me
TLS is a US company now?
This doesn’t restrict TLS, a protocol, it restricts the implementations of TLS by the handful of companies who develop and distribute widely-used web browsers - which are mostly US-headquartered multinationals.
Mandating trusted CAs opens the door to fucking with the communication in progress. Ie undermining TLS whose job it is to protect that communication. Spinning this as an attack on the companies making the browser is a bit too creative for me. That’s like saying wiretaps are an attack on the telco, not the phone calls being listened in on.
Currently browser vendors are able to make their own decisions about which CAs to trust, and how to validate certificates. Most browsers trust a lot of nation states’ CAs, but they (the browser vendors) are currently free to unilaterally stop trusting them when they learn of abuses.
That’s like saying wiretaps are an attack on the telco, not the phone calls being listened in on.
Often it is both. Remember MUSCULAR?
That’s categorically false, they want to inject their own trusted certificates into browsers that’re distributed in the EU, so that any MITM traffic will “just function”. Basically they’re forcing a backdoor for every encrypted channel.
Furthermore they want to make certificate transparency next-to-illegal; remove protections and warnings for when someone is requesting certificates for your domain when you haven’t requested them, plus other uses.
I’m not sure what part of my comment you’re saying is categorically false? I agree with your assessment of eIDAS! I even made a meme about it.
I guess you’re disagreeing with me saying this restricts companies’ implementations of TLS rather than TLS itself? I’m saying that because the law is specifically talking about web browsers, and doesn’t appear to apply to other uses of TLS.
Yeah someone has to (verbally of course) beat the crap out of the people constantly wanting to destroy democracy and privacy…
The EU
There’s the commission and the parliament, and they both usually want different things. And they also consist of different governments and parties.
So, in those two cases, who wants what, specifically? And who opposes what?
eIDAS has been through the trilogues unfortunately, so the Commission, Council and Parliament have reached agreement about it, pending final approval.
The EU is the ultimate centrist. They can be people-friendly, but also corporate-friendly. They’re accused of being a neoliberal for a good reason.
That constant range from pro consumer & privacy friendly to getting wet of having their own surveillance state is pretty bipolar though. I know there’s a lot of politicians & member states that make up the EU apparatus but it’s still weird to see and I really wish the EU would fully embrace the former as there’s really enough intrusive big state entities like that already.
A quick google finds me a government website explaining eidas and what it’s for. By that, I know it’s not behind closed doors or undisclosed, nor requiring compromised certificates.
With a quick google, you might find the same. The eu’s website, are a reliable source for information about the EU I think
You may want to read this: https://last-chance-for-eidas.org/
That’s a lot, I’ll have a better look this afternoon. Here’s my government’s website on this feature
reading further, (summarising) the change is to no longer exclusively trust parties like Google to rule who is and isn’t considered trusted online and instead delegates this to EU member states. This does not affect the use of encryption, or a safe dns provider. No worries about your data being recorded.
However, it does stop large organizations like google and Mozilla from abusing their position of authority to harm competitors availability and trust online
It sounds like you made up your mind in advance to support this. Mozilla (and I believe Google too) have a public and rigorous process to determine which certificates to include in their browser, and, importantly, which not too. This new regulation would enable governments to circumvent that process and force browsers to include their certificates, even if those are used to spy on citizens, or are insecure - like the government of Kazakhstan tried to do before. All this using a process without checks and balances.
Also note that parties like Google aren’t trusted “exclusively” - you can always switch browsers if you don’t trust them. That will no longer be possible with this regulation.
also, last-chance-for appears to be from mozilla and worried about article 45. I can recommend reading it for yourself. If there is one thing I learned in recent years its that orgs funded 95% by google might not be the most trustworthy when talking about internet regulations. So I suggest to not take mozilla by their word, cuz without google funding they’re dead
here is the legal text if you’d like to read
https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=uriserv%3AOJ.L_.2014.257.01.0073.01.ENG
Als je echt Mozilla niet gelooft raad ik u aan om direct deze open brief (dat ondertekend is door meer dan 300 experts) te lezen.
Looks like I might have had an old version of the doc. Clicking the link I read this morning I find a 404. After finding it again, I do find a doc where recognize what they’re concerned about
By that, I know it’s not behind closed doors or undisclosed, nor requiring compromised certificates.
I don’t know how you reached that second conclusion from the fact that there’s a government website, but as https://last-chance-for-eidas.org/ mentions, it was hidden in plain sight, in that eIDAS wasn’t hidden, but the specific consequences were:
Although the deal itself was publicly announced in late June, the announcement doesn’t even mention website certificates, let alone these new provisions. This has made it extremely difficult for civil society, academics and the general public to scrutinize or even be aware of the laws their representatives have signed off on in private meetings.
Did you even bother to google? there’s announcement pages explaining what eidas will be, and the proposal is easy to understand. I have a hunch this is going the same as the “meme ban” did a couple years back
You said you knew there weren’t going to be compromised certificates because there was a government website. But also notice that the kerfuffle is about
New legislative articles, introduced in recent closed-door meetings and not yet public
In other words, these are new additions that are not yet reflected in public documents. This article is also a good explainer.





