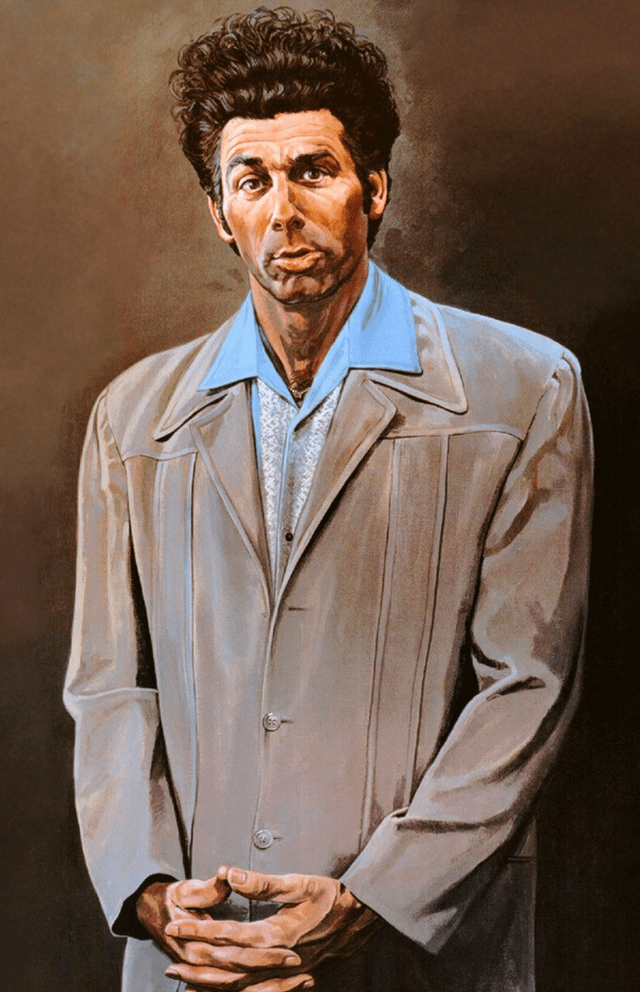
Trivial bugs like this remind me of this:

Can I just believe in my mediocrity instead
The vulnerability is due to “insufficient escaping on the user supplied parameter and lack of sufficient preparation on the existing SQL query,” according to Wordfence.
“This makes it possible for unauthenticated attackers to append additional SQL queries into already existing queries that can be used to extract sensitive information from the database,” the company said.
Ohh yes, little Bobby Tables.
What a convoluted way they chose to say “we didn’t use a prepared statement” lol
Wordfence is a security and vulnerability monitor for Wordpress. The flaw is in the plugin “layerslider”
The plugin is LayerSlider for anyone who is concerned.
However, to exploit the flaw requires a “a time-based blind approach” on the part of attackers to extract database information, which is “an intricate, yet frequently successful method to obtain information from a database when exploiting SQL Injection vulnerabilities,” according to Wordfence.
I wouldn’t call that intricate. It’s pretty standard to try it since you get immidiate feedback that you can inject sql statements.
Again! This kind of thing is why I quit using Wordpress over a decade ago. Static sites don’t have this problem and serve a lot of people’s needs better than a dynamic site.
o the worlds most website builder